Download & Info
Code: Select all
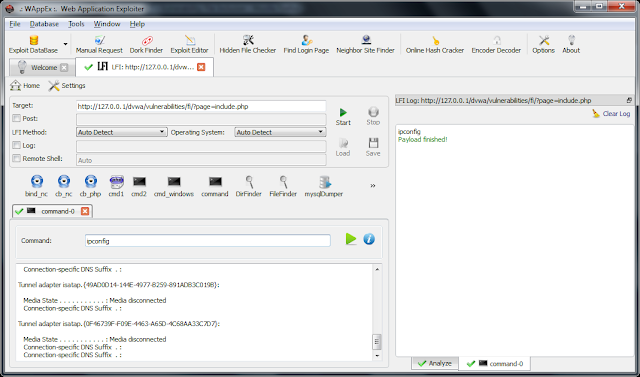
http://www.itsecteam.com/products/web-application-exploiter-wappex/The Exploit Database contains the all the logic associated with trivial fingerprinting, exploitation techniques, and payloads that address a wide range of web application vulnerabilities with the emphasis being on high-risk and zero-day vulnerabilities.
Some of the vulnerabilities already bundled within the Exploit Database include Local File Disclosure (LFD), Local File Inclusion (LFI), Remote File Inclusion (RFI), SQL Injection (SQLI), Remote OS Command Execution (RCE), and Server-side Code Injection (SCI). WAppEx can detect these vulnerabilities in a target, take full advantage of it, and through neatly designed payload codes get as much access to the exploited target as possible in as short a time as possible. Some of the payloads included within the database are various reverse shells, arbitrary code execution, command execution, arbitrary file upload…
Since all the attack logic rests in the form of scripts within the Exploit Database, it is easily extensible, flexible and updatable through community servers. Users, too, can add mature, sophisticated exploits and payloads in the same fashion. The database grows on a daily basis, and our dedicated team of research and development are working non-stop to maintain the richest, most up-to-date aggregate of exploits. The number of exploits is soon bound to surpass hundreds. Meanwhile, users can share their own created exploits and payloads with the community and contribute to this growing momentum.
The scripting language used to create new exploits and payloads is JavaScript with the addition of a few accessory objects and functions that automate daily penetration testing tasks and help integrate the script with the database. Using this feature, you can easily create and execute an exploit based on a newly discovered vulnerability.
WAppEx is also equipped with a penetration testing toolbox that makes an effective synergy with the Exploit Database and a crafty security expert. The provided tools include Manual Request, Exploit Editor, Dork Finder, Hidden File Checker… More tools, such as a crawler, a multi-purpose fuzzer… are to be added to the arsenal in the future releases of WAppEx.
Still, keep your eyes peeled as this is just the beginning of a new, powerful war machine in the pentest battleground.
Updates in 2.0
* Auto-detect feature deleted from exploits
* Browser tool deleted
* Exploits and payloads view changed
* Exploit Database with the following features added:
o New script syntax and structure
o Searching, selecting, and executing of exploits.
o Add/remove database entries (exploits or payloads)
o Add exploits or payloads to the database using either the Exploit Wizard or the script file
o Batch testing of multiple targets against multiple exploits
o Execute multiple instances of one or more payloads (for every running exploit) simultaneously.
* Following tools added:
o Manual Request
o Dork Finder
o Exploit Editor
o Hidden File Checker
o Neighbor Site Finder
* Local File Inclusion analyzer script updated
* 24 new payloads for LFI, RFI, and PHP Code Execution vulnerabilities added:
o Directory Explorer
o CodeExec Bind
o 3 connect-back shells
o Code Execution
o MySQL Dump
o ServerInfo
o 4 command execution payloads
* Bug-fixes:
o Find Login Page crashed on start
o Problem with software registration
o Stop button did not work when retrieving data from SQL server
o Problem with saving SQL results
o Crashed when closing Find Login Page
o Status icons were not displayed properly in exploit tabs
The full list features is as below:
* An exploit database covering a wide range of vulnerabilities.
* A set of tools useful for penetration testing:
o Manual Request
o Dork Finder
o Exploit Editor
o Hidden File Checker
o Neighbor Site Finder
o Find Login Page
o Online Hash Cracker
o Encoder/Decoder
* Execute multiple instances of one or more exploits simultaneously.
* Execute multiple instances of one or more payloads (for every running exploit) simultaneously.
* Test a list of target URL’s against a number of selected exploits.
* Allows you to create your own exploits and payloads and share them online.
* A number of featured exploits (6) and payloads (39) bundled within the software exploit database:
o Testing and exploiting of Local File Inclusion vulnerabilities
o Testing and exploiting of Local File Disclosure vulnerabilities
o Testing and exploiting of Remote File Inclusion vulnerabilities
o Testing and exploiting of SQL Injection vulnerabilities
o Testing and exploiting of Remote Command Execution Inclusion vulnerabilities
o Testing and exploiting of Server-side Code Injection vulnerabilities